One of the most vulnerable resources is an unprotected, installed database server. Database attacks continue to be one of the three most recurring causes of enterprise data breaches year after year, and most of the attacks take advantage of misconfigurations that could have been avoided during initial setup in less than 30 minutes, according to Verizon’s Data Breach Investigations Report.
AlmaLinux 10 is an enterprise Linux distribution based on RHEL with support from Red Hat, and is popular with companies moving away from CentOS. It ships with MariaDB as the default database engine, which is a fully open source, production-proven derivative of MySQL, compatible with MySQL binary-wise, and is maintained by the MariaDB Foundation.
In this guide, you’ll install MariaDB on AlmaLinux 10, implement all critical security hardening tasks, and configure database users that are properly scoped.
What Is MariaDB and Why Is It the Default on AlmaLinux 10?
MariaDB is a community-developed drop-in replacement for MySQL developed by the original MySQL developers since Oracle bought Sun Microsystems in 2010. It is a fully wired protocol compatible with MySQL, which means that any MySQL client, connector, or application can run on it without requiring any changes.
With AlmaLinux 10, the default version of the MariaDB database engine is pre-installed in the official AlmaLinux AppStream repository, as it provides better performance in some workloads, a more active open source community, and a development roadmap that focuses on enterprise reliability. All commands, SQL syntax, and configuration file locations (e.g., /etc/my.cnf) that are discussed in this guide are applicable to both MySQL and MariaDB when using AlmaLinux 10.
Expert Guide: Install and Secure MySQL/MariaDB on AlmaLinux 10
A full installation guide for MySQL/MariaDB, installation of secure authentication, allowing firewall access, and hardening up your AlmaLinux 10 database server. Learn how to properly secure the MySQL/MariaDB database on AlmaLinux 10 systems, including: how to protect the root password, how to remove anonymous users, how to disable remote root access, and how to configure the database for production use.
Step 1: Update the System and Verify the Environment
You should keep your AlmaLinux 10 operating system up-to-date before installing any new server software. If you install on a fully-updated system, you have no uncertainty as to how the new packages will behave, pending kernel updates and security patches:
|
sudo dnf update |
|---|
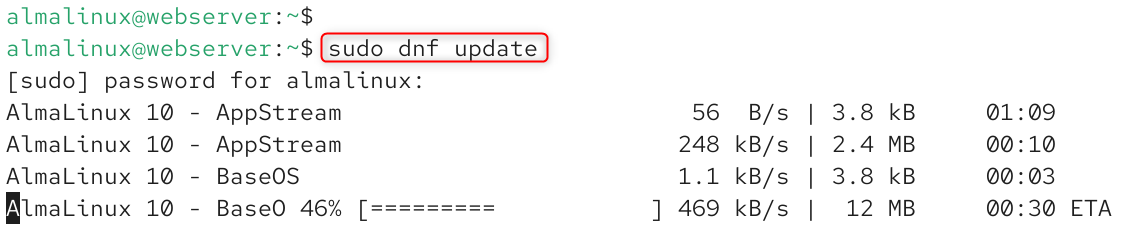
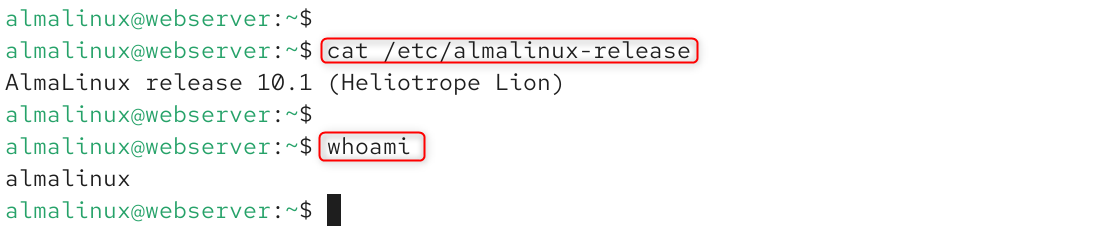
Check your version of AlmaLinux, and ensure you are logged on as a user who has sudo privileges:
|
cat /etc/almalinux-release whoami |
|---|
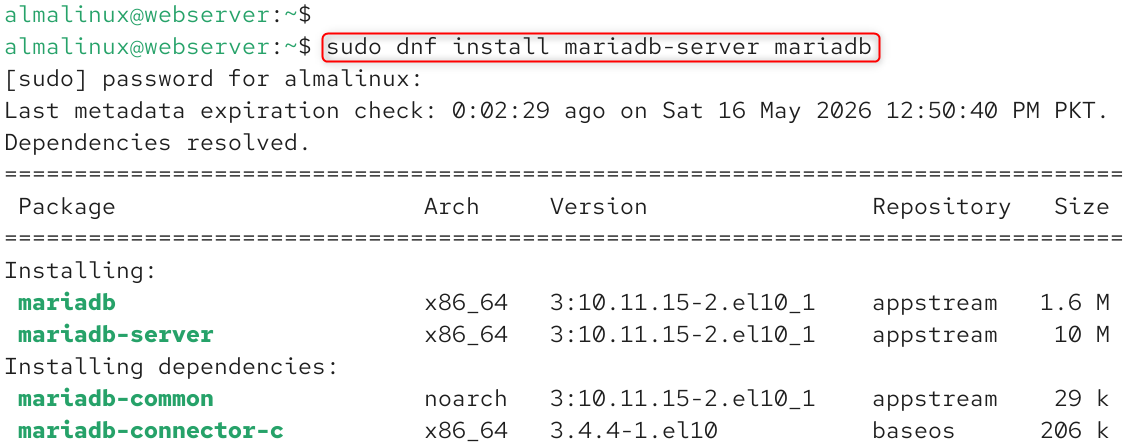
Step 2: Install MariaDB on AlmaLinux 10
MariaDB can be obtained directly from the AlmaLinux 10 AppStream repository. Install both the server and client packages with one dnf command:
|
sudo dnf install mariadb-server mariadb |
|---|
Check the installed version:
|
mariadb –version mysql –version |
|---|
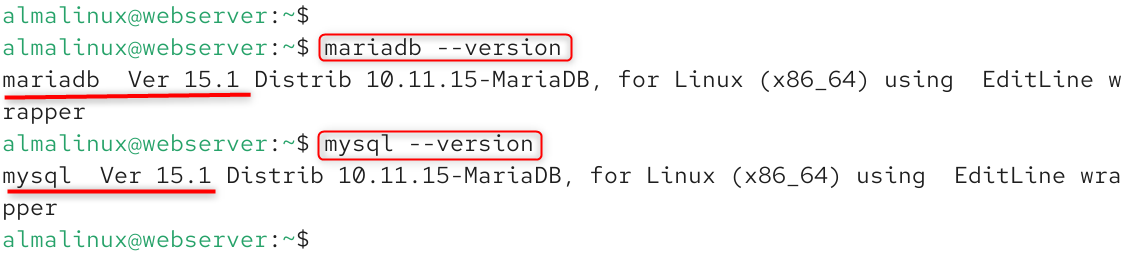
On AlmaLinux 10, both mariadb and mysql execute the same binary, and scripts and tools that are dependent on either command name are backwards compatible.
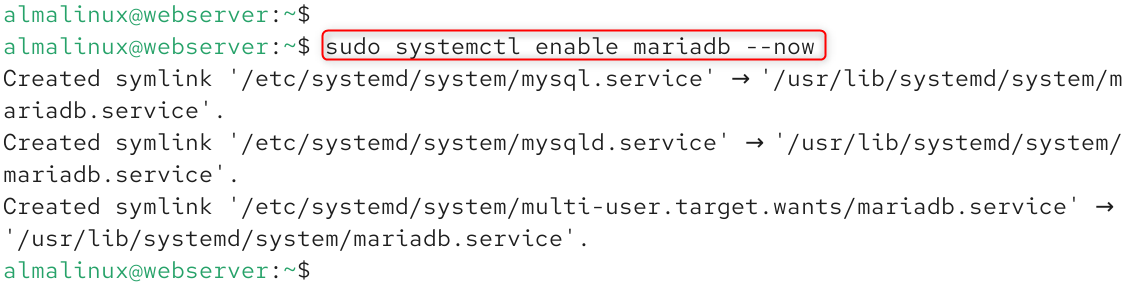
Step 3: Start and Enable the MariaDB Service
Now we can start and enable the MariaDB Service. Start MariaDB, and configure it to start automatically on boot:
|
sudo systemctl enable mariadb –now |
|---|
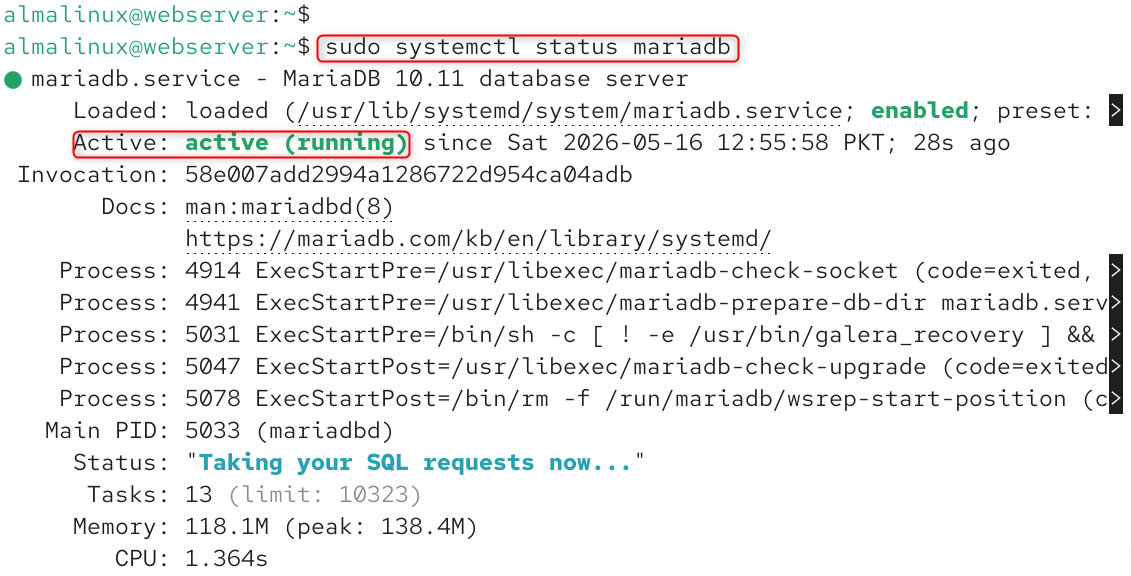
Verify the service is running:
|
sudo systemctl status mariadb |
|---|
Confirm MariaDB is listening on port 3306:
|
ss -tlnp | grep 3306 |
|---|
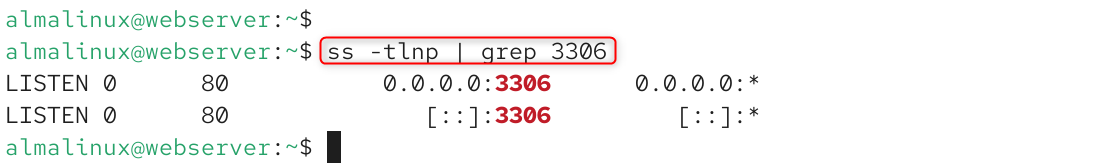
The binding 127.0.0.1:3306 is a crucial security aspect; it guarantees that MariaDB is only accepting connections from the local machine, not from any external network interface.
Step 4: Run the Security Installation Script
MariaDB comes with a security script called mysql_secure_installation, which will ask you questions and guide you through the most important initial steps of securing MariaDB interactively. Run it now:
|
sudo mysql_secure_installation |
|---|
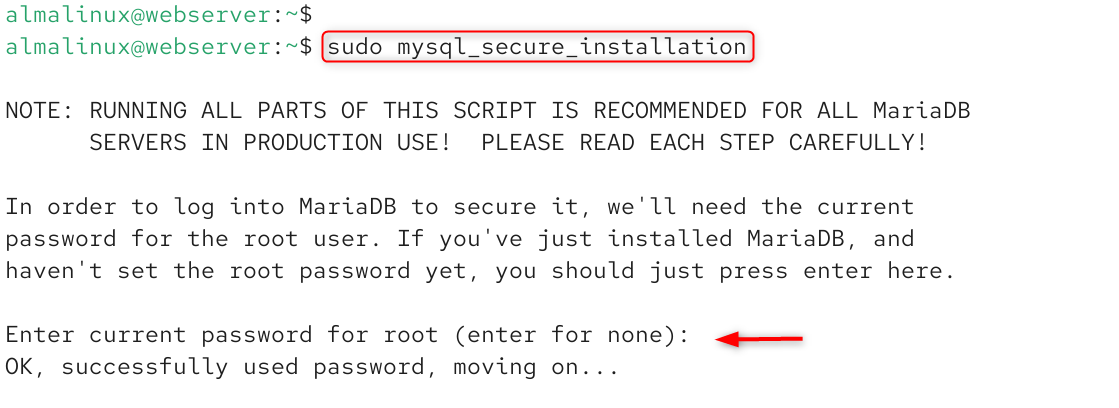
The following prompts are given in the script. These are the proper answers for a production server: You will be presented with the root password. You will be asked for the current root password.
If you answer Y to “Remove anonymous users”, any account that allows anyone to log in to MariaDB without a password will be deleted, something that is not acceptable on any server that is connected to a network. If you set the answer to Y for “Disallow root login remotely,” then even if an attacker knows the root password, he cannot log in to the system remotely. If you choose Y for “Remove test database”, you will get rid of a publicly writable database supplied by default, which is a known attack surface for which there are several CVEs.
Step 5: Verify Security Hardening Applied
Once you have run mysql_secure_installation, check that every security step was executed properly by directly checking the MariaDB system tables:
|
mysql -u root -p |
|---|
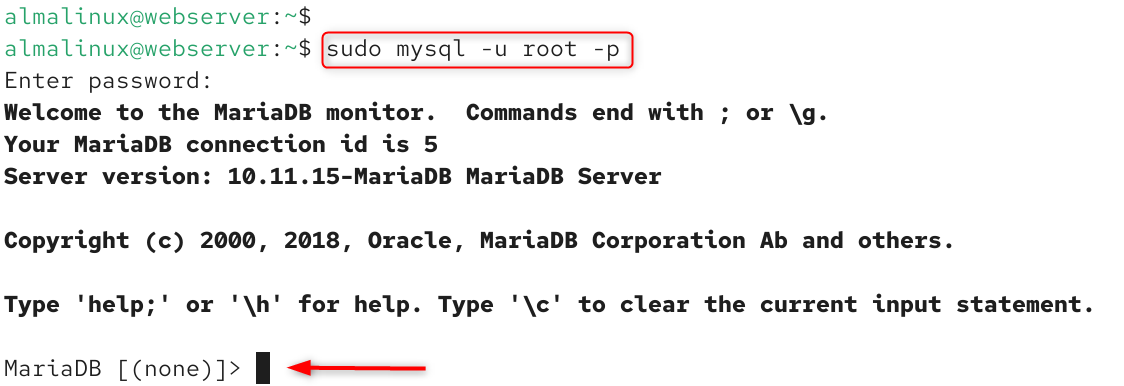
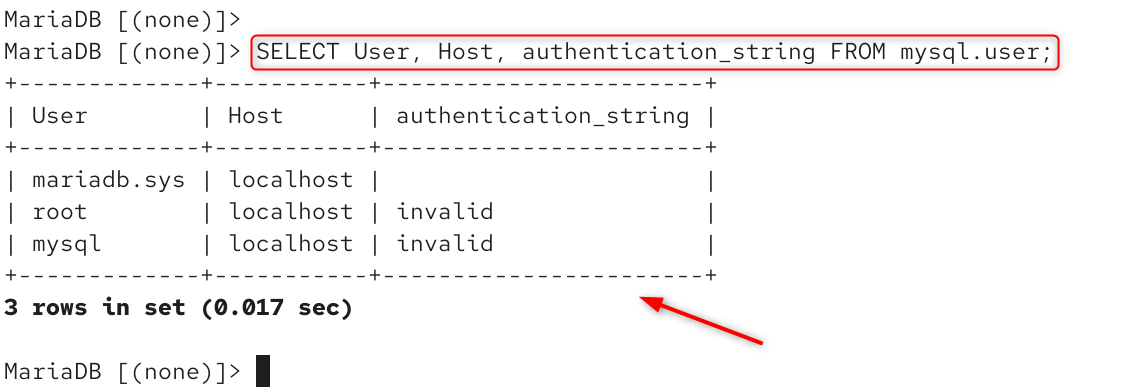
Use the MariaDB shell to run these verification queries. Run the following command to check all users/password status:
|
SELECT User, Host, authentication_string FROM mysql.user; |
|---|
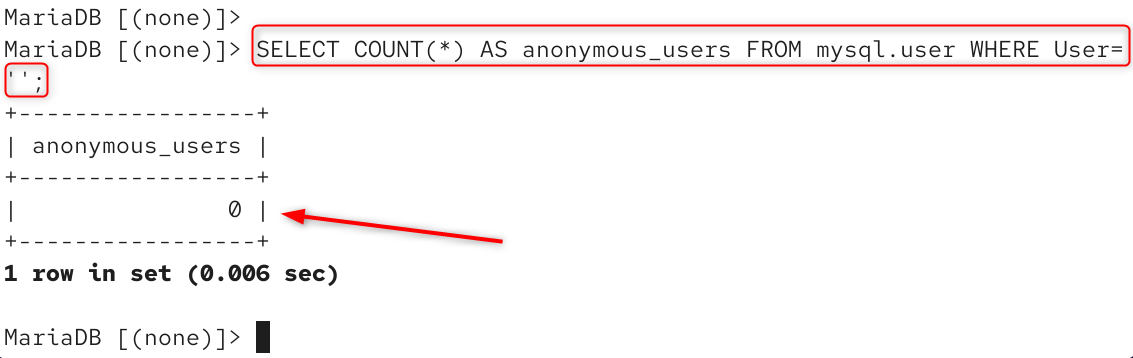
Verify: 0 anonymous users
|
SELECT COUNT(*) AS anonymous_users FROM mysql.user WHERE User=”; |
|---|
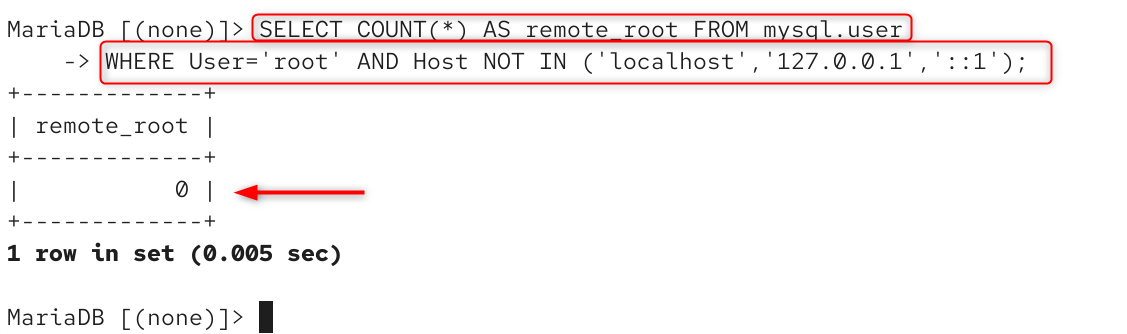
Verify: 0 remote root access
|
SELECT COUNT(*) AS remote_root FROM mysql.user WHERE User=’root’ AND Host NOT IN (‘localhost’,’127.0.0.1′,’::1′); |
|---|
Verify: test database removed
|
SELECT COUNT(*) AS test_db FROM information_schema.SCHEMATA WHERE SCHEMA_NAME=’test’; |
|---|
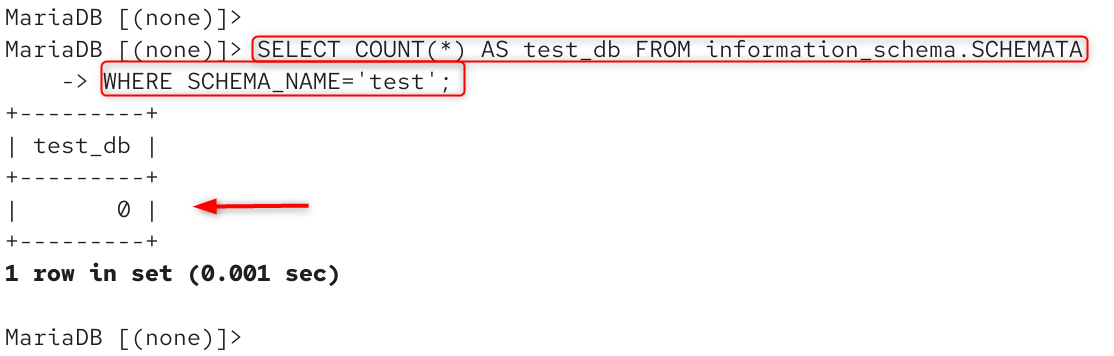
The three checks return the appropriate results: zero anonymous users, zero remote root access, and zero test databases. You have now hardened your MariaDB installation.
Step 6: Create a Dedicated Application Database and User
The most common and risky misconfiguration of MariaDB is to allow apps to log in directly to the root account. The root user has complete access to all databases on the server. If an application with root access is compromised, the attacker immediately has all access rights to all databases.
The proper way is to establish a separate database and assign a dedicated user to it with just the necessary level of access for that application:
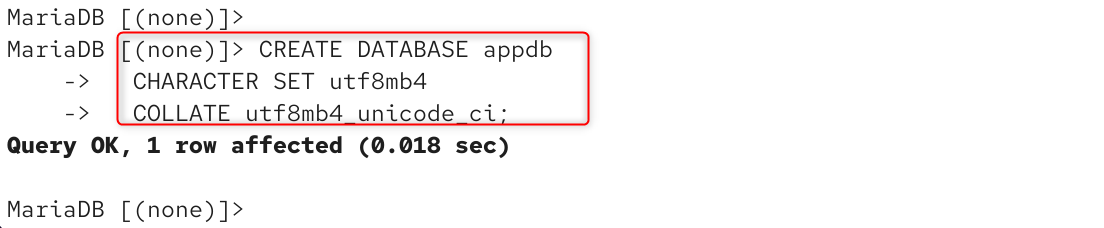
Create the application database with UTF-8 encoding.
|
CREATE DATABASE appdb CHARACTER SET utf8mb4 COLLATE utf8mb4_unicode_ci; |
|---|
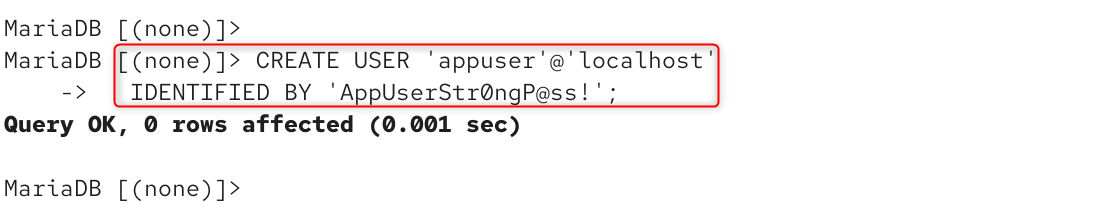
Create a dedicated application user.
|
CREATE USER ‘appuser’@’localhost’ IDENTIFIED BY ‘AppUserStr0ngP@ss!’; |
|---|
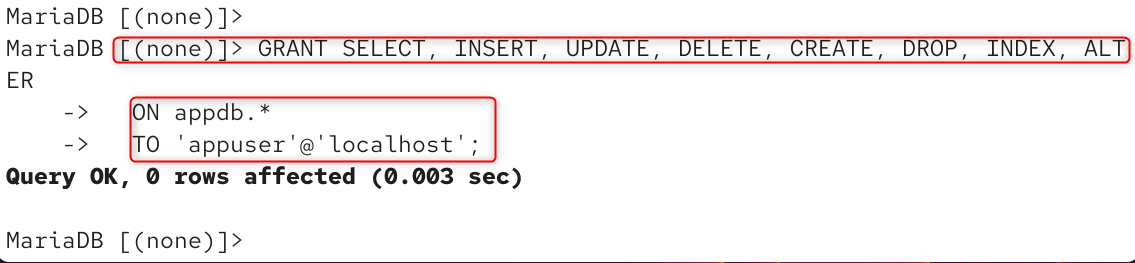
Grant only the privileges this application actually needs.
|
GRANT SELECT, INSERT, UPDATE, DELETE, CREATE, DROP, INDEX, ALTER ON appdb.* TO ‘appuser’@’localhost’; |
|---|
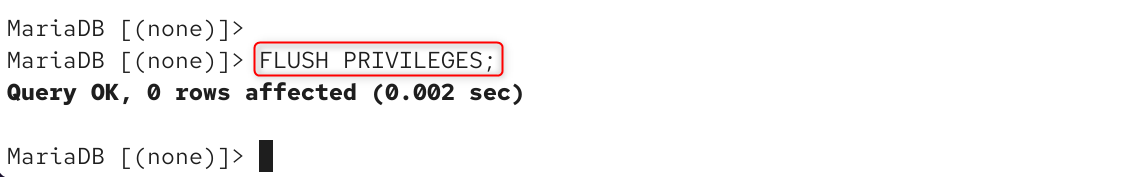
Apply the privilege changes immediately.
|
FLUSH PRIVILEGES; |
|---|
Verify the grants were applied correctly:
|
SHOW GRANTS FOR ‘appuser’@’localhost’; |
|---|
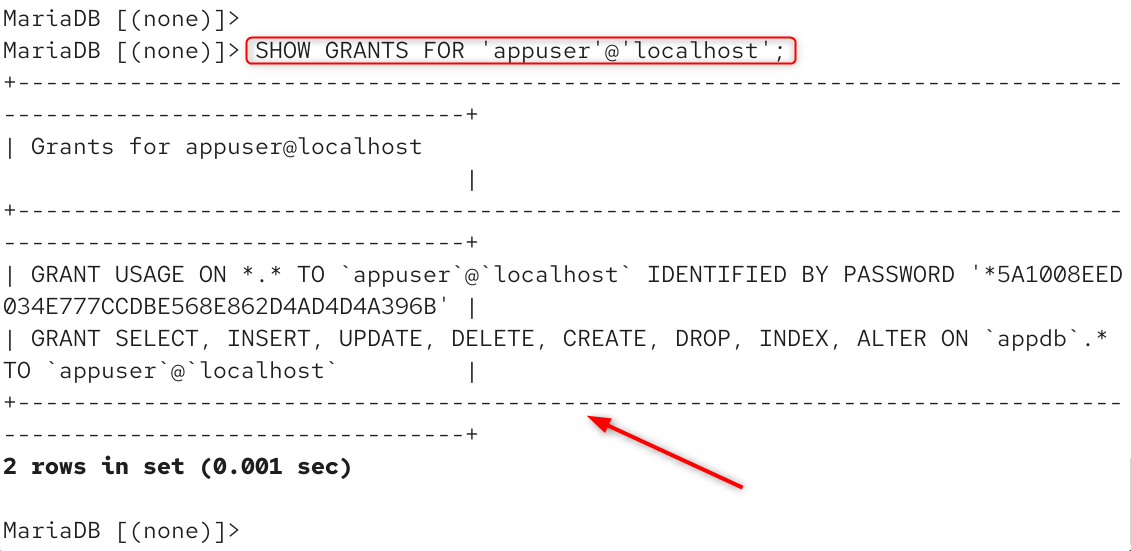
The first line contains GRANT USAGE ON *.* — MariaDB does not allow the user to be created without having any privileges whatsoever. All permissions are given only to the appdb database, following the principle of least privilege.
Step 7: Test the Application User’s Database Access
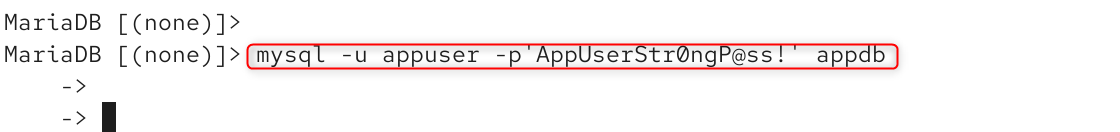
Check if the appuser can connect to their database and can execute operations:
|
mysql -u appuser -p’AppUserStr0ngP@ss!’ appdb |
|---|
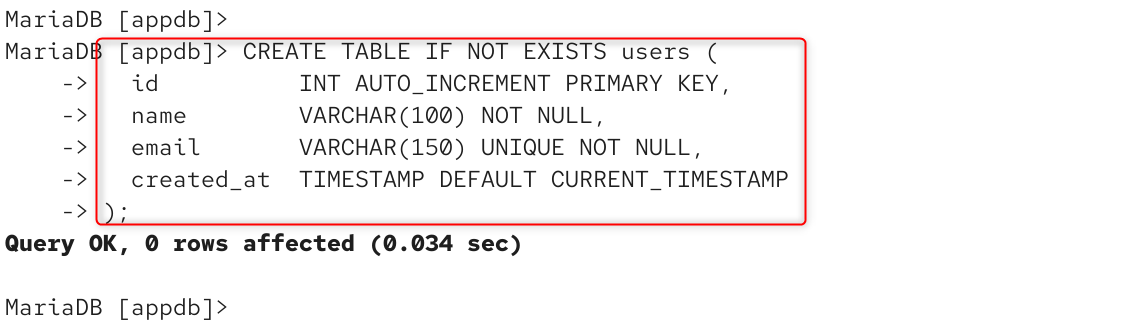
Create a real application table.
|
CREATE TABLE IF NOT EXISTS users ( id INT AUTO_INCREMENT PRIMARY KEY, name VARCHAR(100) NOT NULL, email VARCHAR(150) UNIQUE NOT NULL, created_at TIMESTAMP DEFAULT CURRENT_TIMESTAMP ); |
|---|
Insert test records
|
INSERT INTO users (name, email) VALUES (‘Alice Johnson’, ‘alice@example.com’), (‘Bob Smith’, ‘bob@example.com’); |
|---|
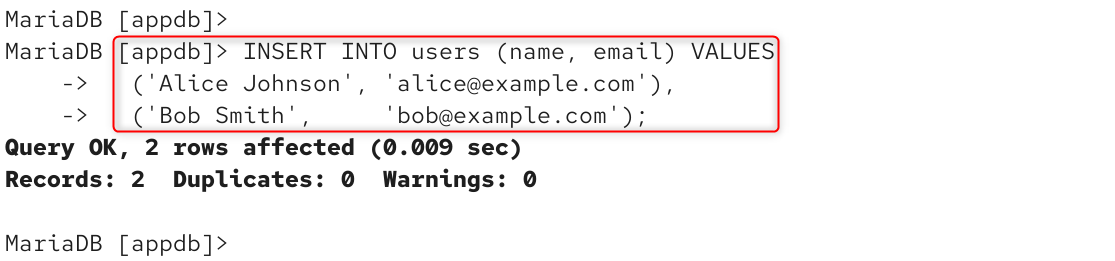
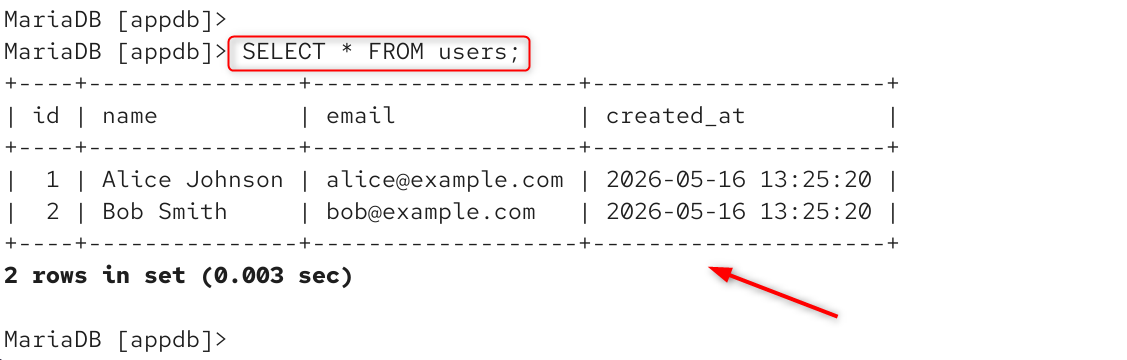
Query the data
|
SELECT * FROM users; |
|---|
Ensure that appuser is unable to access system databases: This will stop privilege escalation in the event of a compromise of the application:
|
USE mysql; |
|---|
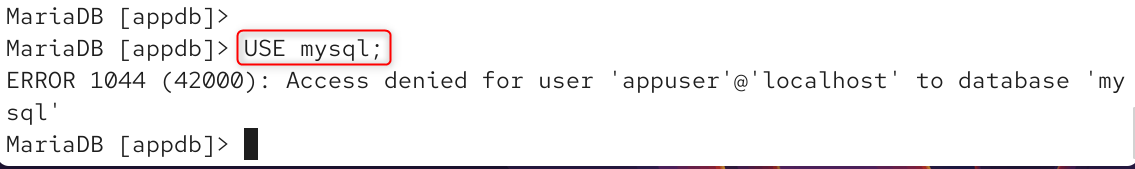
The access denied error confirms that the privilege scoping is working correctly.
Step 8: Configure the Firewall on AlmaLinux 10
AlmaLinux 10 uses firewalld as its default firewall manager. Since MariaDB is bound to 127.0.0.1 and should never accept external connections in a standard single-server setup, verify that port 3306 is not publicly exposed:
|
sudo firewall-cmd –list-all |
|---|
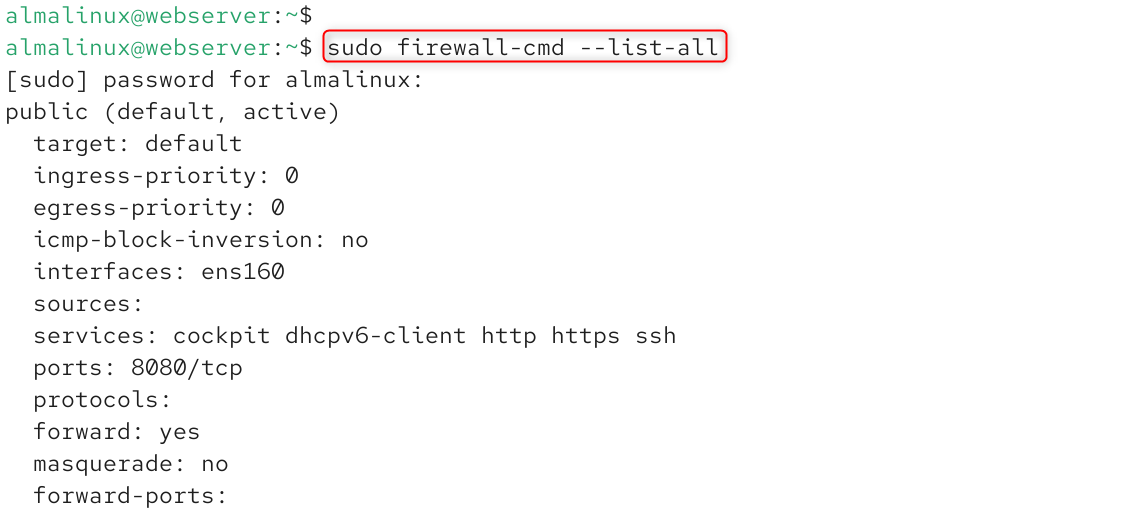
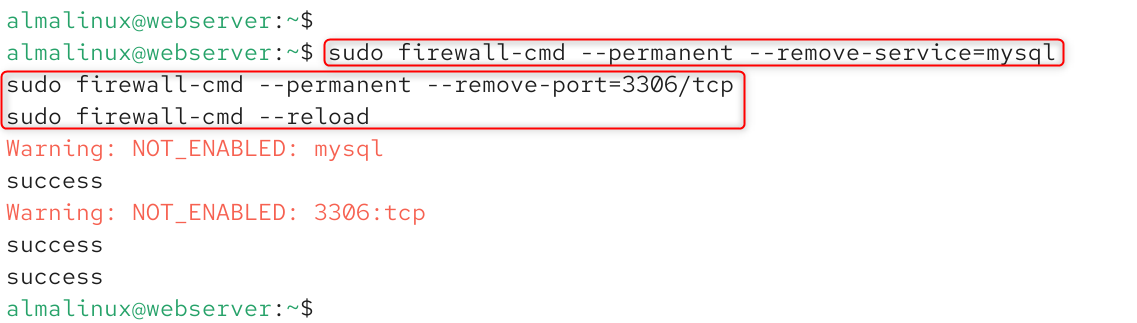
If port 3306 appears in the output, remove it immediately:
|
sudo firewall-cmd –permanent –remove-service=mysql sudo firewall-cmd –permanent –remove-port=3306/tcp sudo firewall-cmd –reload |
|---|
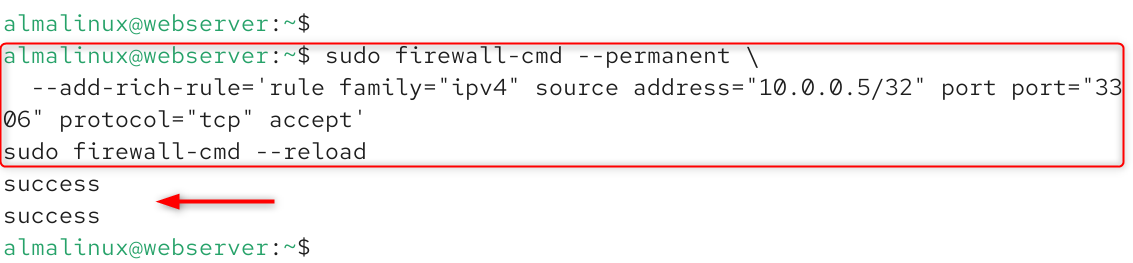
If your architecture requires a remote database connection — for example, a web server on a private network connecting to a dedicated database server — open port 3306 only to the specific trusted IP address, never to the entire internet:
|
sudo firewall-cmd –permanent \ –add-rich-rule=’rule family=”ipv4″ source address=”10.0.0.5/32″ port port=”3306″ protocol=”tcp” accept’ sudo firewall-cmd –reload |
|---|
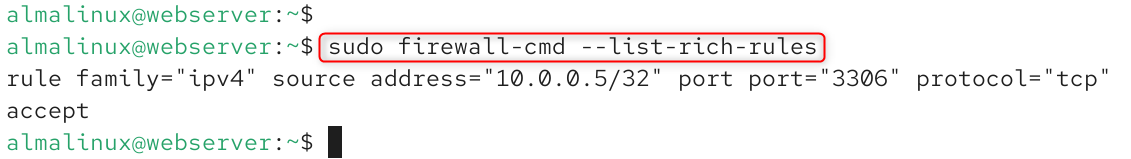
Verify the rule was applied:
|
sudo firewall-cmd –list-rich-rules |
|---|
Troubleshooting Common Issues on AlmaLinux 10
Using AlmaLinux 10, this guide covers common problems and how to fix them.
- Cannot connect as root after mysql_secure_installation. On AlmaLinux 10 and MariaDB 10.11, the root user logs in by default using Unix socket authentication. Use sudo mysql or mysql -u root -p from the “root” account of the OS. If you must log in as root, run: ALTER USER ‘root’@’localhost’ IDENTIFIED VIA mysql_native_password USING PASSWORD(‘yourpassword’);
- MariaDB fails to start after editing the configuration file. Check the syntax of your configuration file before restarting it with mysqld –help –verbose 2>&1 | head -20. If you find any syntax errors in the configuration file, MariaDB cannot start, and the syntax error is reported in /var/log/mariadb/mariadb.log.
- Access denied for user ‘appuser.’ This is because either the password is incorrect, or the user is attempting to log in from a host different from the one in the CREATE USER statement, or FLUSH PRIVILEGES was not executed after the grant statement. Check with: SELECT User, Host FROM mysql.user WHERE User=’appuser’;
- Port 3306 appears in external network scans. This means that bind-address is not properly configured to 127.0.0.1, or that there is a rule in the firewalld configuration that allows port 3306. Check with sudo firewall-cmd –list-all and verify ss -tlnp | grep 3306 shows 127.0.0.1:3306, not 0.0.0.0:3306.
Conclusion
On AlmaLinux 10, install MariaDB using dnf with the commands: sudo dnf install mariadb-server mariadb and then sudo systemctl enable –now mariadb to start it. Execute sudo mysql_secure_installation and follow the prompts to set a password for the root user, drop anonymous users, and disable remote access to root. You’ve done everything that was recommended to make MariaDB 10.11 as secure as possible, created the application user with the minimum privileges, hardened the configuration file, and ensured that only port 3306 is accessible on the firewall.





Leave feedback about this